Authenticity will be as big as the internet itself.
That means big opportunity for YOU.
Things are not working.
Your customers or audience members are suffering from phishing attacks, malware, fraud, privacy invasion – all sorts of digital mayhem.
They’ve been told that solving those problems calls for constantly increasing spending and effort – using security technology that’s not working!
That’s nothing new. As MIT noted in 2006:

THE INTERNET IS BROKEN.
And of course it’s still broken. And getting worse
Spam brings us phishing attacks that deliver malware that in turn builds botnets. Fraud and predation pervade everyday online experience. Identities - and cash - are stolen in batches.
While the security industry assures us “we're working on it,” people grow ever more wary of their Internet experience - even as they come to depend upon it more and more.
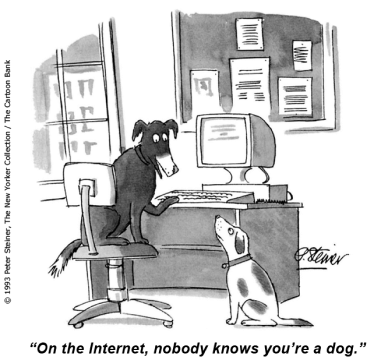
All those security problems are an effect of a bigger problem, and that problem is inauthenticity.
People and sites are not who and what they claim to be.
The other side of that coin is that if you solve inauthenticity then you solve a lot of other problems. Security is just one of them. And if you solve inauthenticity you bring new convenience and value to the lives of people in your audience everywhere.
Real Security
After spending millions of dollars on network security, corporations still have major security problems.
Meanwhile, your ATM card allows your bank to dispense cash with confidence from a machine on a city sidewalk.
The technology used by your ATM card is more ancient than the floppy disk. So why are bank ATM networks generally secure, while corporate information networks, in spite of continuous investment in the latest security technology, are barely able to keep ahead of intruders?
The difference is not about technology. The difference is about assumptions.
Your bank's ATM network starts with the premise that knowing who you are is the foundation of security.
If a trusted co-worker asked you to share your ATM card and associated PIN, what would you say? Of course, they'd never ask in the first place.
If that co-worker asked you for your network password, what would you say? In many companies, collaborative work gets done by sharing access credentials, in spite of rules against it.

The illusion of security
Right now, you’re in a "secure" space. The https:// on this site’s address means that the connection between your computer and ours is quite secure.
While you're here, our computer knows that yours is the one that started this session, yours knows the same thing about ours, and we have the mutual comfort of knowing that intruders on our conversation can neither decipher nor alter its content.
Now let's talk about people, not computers.
Do you know who we are?
Do we know who you are?
We only know that the computers that started this session have not changed. We know nothing about the people operating those computers.
We have to take a lot on faith.
Faith is not a good basis for matters of identity in online environments.
Despite the lock icon on your browser, despite the SSL behind this session, we need to do more for this connection to be secure.
Almost all security technology is built upon the assumption that it’s possible to determine the intentions and character of the sender of a stream of bits.
The Zero Trust Model was introduced in
344BCE
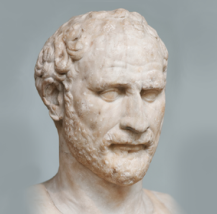
That’s when Demosthenes advised
“There is one safeguard which all sensible men [and women] possess by nature.
It is Distrust.
Guard this possession and you will never fear disaster.”
Do you think that’s possible?
Imagine telling a building lobby receptionist, "Please determine the intentions of everyone who enters the building, and also determine whether they are good or bad people.
If you think that's an unreasonable request, and if you know how a building works, then you are better prepared to judge security approaches than the security experts are.
Instead of course we ask receptionists to get some form of identity from the visitor. Managers of physical spaces know that real security is about accountability. It’s not about cops-and-robbers games, trying to identify perpetrators by appearances.
The alarming fact is that managers of physical spaces better understand the fundamental assumptions that should guide digital security than do managers of digital spaces.
Current security technology is mostly about determining the intentions and character of the sender of a stream of bits.
Problem: in most cases that is impossible.
When it is possible, it's because the intruder lacks skills or funding. In other words, security products tend to deter the least threatening attacks. That renders mainstream information security efforts ineffective or even useless.
Keep me posted about Authenticity
That gap in understanding means opportunity for you!
Authenticity™ Works Where Security Technology Has Failed Us.
See the “Our Enterprises” tab to learn about the many opportunities to create value by bringing Authenticity to the market where your good reputation has been built on strong performance.
Learn how you can be the one to bring Authenticity to the market you’re familiar with...
By establishing measurably reliable identities
By designing and building online spaces upon a foundation of reliable identities, PKI Done Right™, and InDoor™ standards and practices

